The Alignment Between Netops and DevOps Roles
Infrastructure as code (IaC) enables DevOps teams to manage an application’s operational environment throughout the development and testing phases via automation and self-service. DevOps best practices were constructed from IaC projects. Adaptive applications leveraging next-generation application-centric view enablement follows the DevOps blueprint with IaC.
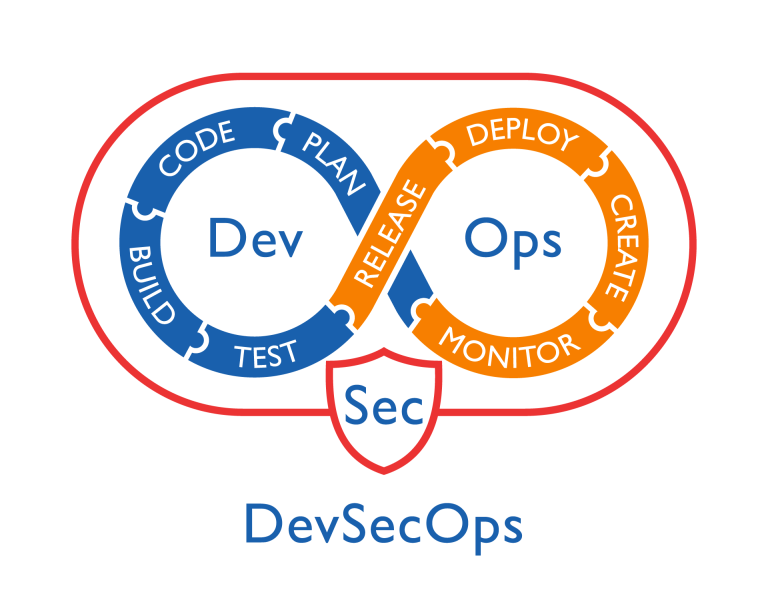
IaC helps organizations with their digital transformation journey through developing modern applications based on agile development, not a waterfall framework. Greater performance of applications and application protection is recognized early in the development cycle under DevOps agility. Security functions become enabled at each stage of development instead of at the end of the creation cycle.
The DevOps Movement
DevOps became successful without significant networking involvement. Traditionally, when development teams finish building applications, they move the project to the networking team, who then begins to manually configure each server for deployment. The security department operated independently from the rest of the company, and rarely have an input in the application development lifecycle.
By shifting networking left in the continuous integration continuous delivery (CI/CD) pipeline, NetOps helps increase efficiency in the software development lifecycle (SDLC) and minimizes late-stage deployment problems.
Moving Ahead To The DevOps Culture
IT departments in the late 1990s and early 2000s were structured similar to the Open Systems Interconnection (OSI) model.
Well structured for its time, this model proved to lack the flexibility to adjust to the changing business climate. Each department would only focus on their part of the “stack” and quickly pass responsibility to other groups.
Change control became a struggle for organizations within the traditional IT stack. Simple changes require downstream and upstream communication, testing, and production validation. Often, a small application change could require a significant firewall change or a network topology costing the company money and time. In many cases, simple delays could take months to execute.
After 2008, when cybersecurity events became daily business impacts, companies needed to become flexible, nimble, and quick to react to stay up with the competitive market and hackers.
Everything about DevOps changed the company’s culture around information technology operations.
DevOps is all about “being flexible.”
Rapid Adoption Of The DevOps Culture
Sub-groups or scrums are created from the traditional IT model. Previous IT security team members become the SecOps team. The application teams became part of the application owners group. NetOps teams are formed from the legacy telecom and network teams.
Be A Member Of A Scrum
Being a member of the team is critical to success in cybersecurity. Being a member of the scrum is all about teaming, collaboration, and contributing to the organization’s effort to develop products and solve complex business objectives while protecting the company from cyber breaches.
Learn To Be A Scrum-Traveler
Travelers are subject matter experts with experience in specific domains. These experts move between various scrum teams and support multiple projects.
Candidates become valuable to any organization through continuous learning, experience, and collaboration. Being a scrum-traveler helps organizations leverage their talents between various components within the Agile development model. In one week, the scrum-traveler could be at the front-end of a new project sprint cycle providing expertise in security within a Microsoft platform. The following week, the traveler could be involved in several sprints around the quality assurance of a new solution. Every investment in learning cybersecurity will pay off for each candidate. The more the candidate invests in knowledge, the more significant opportunity to serve the organization.
Both reported to a scrum leader. Scrum leaders would be accountable for the project’s success and be responsible for sprint execution.
Unifying IT: The Convergence of DevOps, SecOps, and NetOps
In the spirit of the DevOps movement is a need for digital transformation change. Risk management, pen-testing, and vulnerability scanning should be considered a “sprint” within the agile security model supporting threat modeling engagements. Small to mid-size enterprise organizations could save money while gaining greater insight into their environment by executing these audits into a unified project instead of silo (waterfall) work cycles. The true benefactor of this new model would be the risk management team. By pulling together outputs from these “sprints” into a centralized contextual risk scoring methodology, organizations will better assess the environment by cross-correlation data sources from pen-testing, scanning, and IT audit control reviews.
All cybersecurity current and future professionals should be well-versed on each OPS term and their relationship to each other. Gone are the days of silo IT and waterfall methodologies. The future of IT is DevOps, SecOps, NetOps, NetSecOps, and DevsecOps.
This shift towards integrated, agile methodologies is not just a trend, but a necessary evolution to meet the demands of modern digital transformation. At CIAT, we recognize the importance of preparing the next generation of IT professionals for this new reality. Our software development programs are designed to equip students with the skills needed to thrive in these dynamic environments. Whether you’re interested in becoming a DevOps engineer, a security specialist, or a full-stack developer, CIAT offers tailored programs to help you succeed in the interconnected world of modern IT operations. Aspiring IT professionals can learn to drive innovation, enhance security, and create more efficient, responsive technology ecosystems by enrolling in our Assosicate’s or Bachelor’s of Applied Science in Software Development today!
The future of IT is collaborative, agile, and integrated – and at CIAT, we’re committed to helping you be a part of it.